As smartphones have become smarter, they have become filled with more and more data that needs to be kept private for the owner’s safety and security. This is why it is fortunate that there are also more ways to secure a smartphone against unauthorized use. We’ll examine the many options to devise which is the most secure.
Tech Minutes
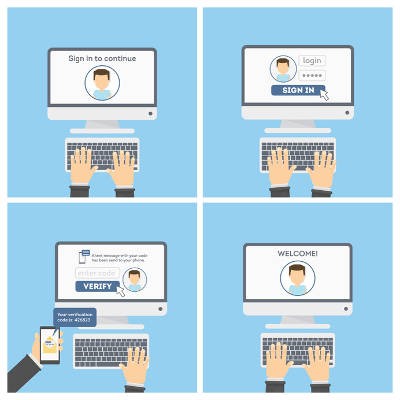
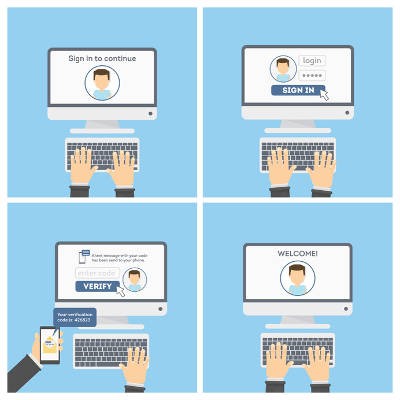
2FA, or two-factor authentication, is a simple and effective means of boosting your cybersecurity. Despite this, a study performed by Duo Labs suggests that 2FA has not been adopted as much as one might expect, or as much as it should be.
2018 could potentially be a big year for your business. However, your business needs to be around long enough to see any positives that may come its way, which means you need to be prepared for the negatives. Here are five resolutions for you to make this year to help preserve your organization’s cybersecurity.
Data security has to be a core consideration of the modern business, so every small effort you can take to protect your business is important. One such effort is the implementation of two-factor authentication. However, your employees may not initially feel entirely comfortable with some facets of two-factor authentication.
You’re lucky to go a month without seeing news of some devastating data breach. With more businesses gearing up for the worst, what are you doing to protect your organization’s intellectual property and sensitive data? You can start by implementing a new type of authentication system that’s much more secure than your current security strategy--two-factor authentication.
 Hackers are growing bolder by the day, taking on huge organizations like the IRS and Sony Entertainment, and forcing businesses to stay on the defensive at all times. In spite of this, what can the average small business do to keep themselves safe? For starters, you can integrate multi-factor authentication, a solution designed to make it extra difficult for hackers to access online accounts.
Hackers are growing bolder by the day, taking on huge organizations like the IRS and Sony Entertainment, and forcing businesses to stay on the defensive at all times. In spite of this, what can the average small business do to keep themselves safe? For starters, you can integrate multi-factor authentication, a solution designed to make it extra difficult for hackers to access online accounts.
 In this day and age, a password isn’t enough to keep your accounts secure from attempted hacks. Passwords can be cracked as easily as anything. A lot of businesses have moved to two-factor authentication in order to preserve their data. There are several ways of using this for your business, but a new startup called BioCatch is developing an authentication procedure which looks at your mouse activity.
In this day and age, a password isn’t enough to keep your accounts secure from attempted hacks. Passwords can be cracked as easily as anything. A lot of businesses have moved to two-factor authentication in order to preserve their data. There are several ways of using this for your business, but a new startup called BioCatch is developing an authentication procedure which looks at your mouse activity.