For a lot of businesses, employee mobile phone usage was once a big problem for them. There have been some businesses that actually hired someone to walk around their office telling people to get off their phones. Some businesses outlawed employee devices altogether. There probably are some businesses out there that still limit the use of these devices in their office, but for most businesses, their employees’ smartphones are now completely part of their productivity strategy. Let’s take a quick look at the shift from banned to benefit in this month’s newsletter.
Directive Blog
You might see 3G and 4G on your mobile devices and wonder what it all means. If so, we have an answer for you, and just in time for a brand-new iteration: 5G. With this new technology on its way, it’s time to take a look at what exactly 5G should be capable of, and how it can differentiate itself from its predecessors.
Does your business have trouble with managing and maintaining your technology? If so, you’re not alone. Many small businesses struggle with even the most basic elements of IT maintenance. Wouldn’t it be nice if you could just take this responsibility and shift it off of your employees? The best way to approach technology maintenance is to implement managed IT services.
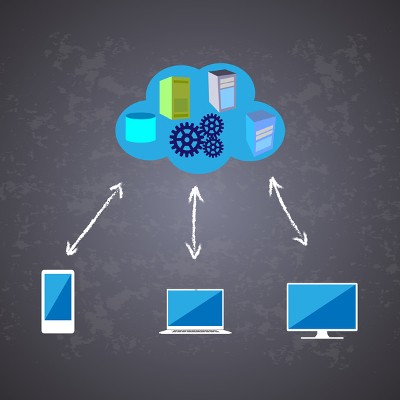
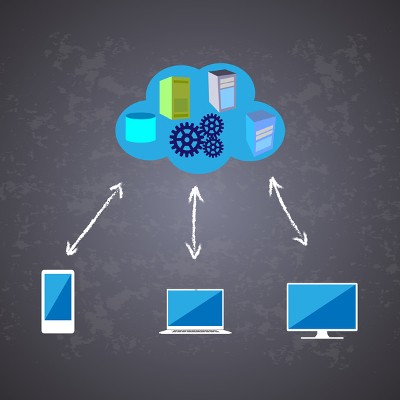
Your business relies on technology to ensure operations proceed smoothly, but the way that it’s managed can have a major impact on the way your company functions. Think about it like this: if you have software solutions hosted on different computers, but not in any centralized location, only those computers will be able to use these solutions--potentially hampering your staff’s ability to be productive. How can you make sure that this doesn’t become a major problem?
We are going to switch things up a bit and walk you through a retelling of a ransomware attack through the eyes of a business owner. Usually when we talk about these types of threats, we approach it from our perspective and talk about what you should do to prepare and what the threats are, but we wanted to try to show you what an event like this could feel like, for you, in your position, and in your own eyes. We hope that this will raise awareness of how crippling an event like this can be on your company, and we hope you let us know if this perspective helps you, your colleagues, and your staff get a more personal sense of what ransomware can do. Enjoy!
Ransomware is a growing problem for businesses, being one of the most difficult threats to remove from an infrastructure. Not only is it easy to spread, but difficult to avoid as a whole. How can your organization prepare for this threat? It starts by being mindful of how ransomware is spread and how your employees react to it, both now and in the future.
Every business needs technology support. This statement is more true today than it has ever been before. As your organization adds new technology to its infrastructure, it will naturally grow more complex and difficult to maintain. Thankfully, you don’t necessarily have to go about this alone. By working with an outsourced third party, your business can take advantage of all kinds of great solutions for a fraction of the cost.
Cloud computing is one of the best ways that your business can compete with larger enterprises. Today, you can adopt the cloud and take advantage of countless services, but are you doing so yet? If not, we’ll help walk you through some of the best ways that your organization can leverage the cloud.
The sad truth about computers is that when they inevitably break, you have to get them fixed; or, you have to order a new one. When PCs started to be utilized for mass productivity, however, businesses had to find a better way. It’s been years since the first managed services provider hung out their shingle, and over that relatively short time the managed services industry has grown to be a $150 billion-a-year industry. The combination of IT becoming an important part of nearly every business resulted in the obvious demand for affordable IT support. This trend has seen many businesses cutting IT staff to make way for outsourced managed services, and all it provides. A problem that both businesses, and the MSPs that they hire, face is that computers eventually break.
For the modern business owner or executive, making smart business decisions has become a necessity. Margins are small, efficiency is key, and if we were to be completely honest, business is a day-in and day-out grind. In the course of doing business much is made of cost reduction and curtailing inefficiencies that lead to wasted capital. Much is made of collaborative systems that allow for remote access. Much is made of protocol, process, and performance. With so many moving parts in every business, there has to be the “glue” that allows for cohesive actions to be taken. That “glue” is software.
How much does your business rely on technology to keep your organization running forward? As business technology becomes more complex, it’s becoming increasingly popular for organizations to have their own internal IT departments to manage and maintain it. Yet, small businesses don’t often have the necessary funds for such a feat. How can your company afford quality IT service? You can start by pursuing managed IT solutions from a managed service provider.
How many documents does your organization accumulate just by simply staying in business? There’s no doubt that you’re sick of the traditional filing cabinet, which is both hard to move around and a pain to organize. Thankfully, modern technology solutions have afforded businesses just like yours with the ability to host and manage documents in a digital, cloud-based environment.
Small businesses often have to rely on different means to achieve the same level of project management as enterprises. This is due to the demands of project management being significantly different in scope, but also the way that your company implements new technology solutions. Instead of worrying about the specifics of project management, you can outsource these responsibilities to a managed service provider.
Data is the backbone of any modern business. Since your organization relies so much on it, you need to have measures put into place to ensure that your business can access it in some way, shape or form at all times. This is easier said than done, especially for a business on a budget. We’ll walk you through how you can implement a comprehensive data backup solution to protect your organization.
Your business relies on its technology being maintained properly, but it’s not always as simple as updating a software application or replacing a hard drive following a catastrophic failure. You have to think about who you’re paying to maintain your technology solutions, if there’s anyone doing it at all. You need to consider what happens when you lose data or when your organization experiences downtime. How do you keep technology from becoming a hindrance for your business?
How does your business manage its technology solutions? If you have an in-house IT department, you might think that you have a better shot at keeping your business safe from a hard drive failure, but this is only if your IT department isn’t already overwhelmed with work. You might find that implementing new solutions is tricky, which wastes time and resources on your part. What’s the small business to do?
Communication is one of the cornerstones on which your business functions, and without it, you will find that going about your daily duties is considerably more difficult. Communication is one of the many ways your organization accomplishes both major and minor tasks, so you want to pay especially close attention to how your business handles phone calls, email, and even mobile devices--both in and out of the office.
Building a social media strategy can be somewhat troublesome for the modern business. Not only do you not know how it can affect your organization, you also know that your competitors are likely using it. To this end, we’ll go over how your organization’s social media practices can influence success.
Security is an aspect of running a business that absolutely cannot be ignored, regardless of whether or not you see it as a considerable issue in the near future. The fact remains that your organization will always be at risk unless you take actions to keep it safe today. By taking advantage of some of the latest and greatest security tools on the market, you’ll be able to protect not only from the basic threats, but more advanced ones as well.
Businesses today rely on so much technology that it’s impossible to think about operations without considering how technology can make them more efficient. In fact, many organizations would completely collapse without the innovations brought about as a result of technology development. One of the hottest trends over the past few years has been the shift from in-house assets to web-based assets, ranging from application access to infrastructure hosting.
People spend a lot of money on the Internet. From an individual standpoint, the amount the average person spends on Internet-based services is their largest expense outside of the money they spend on their residence, and perhaps their transportation costs. In order to understand the landscape of what is effectively a battle for Internet supremacy, you first have to take a look at the battlefield itself.
Your data is one of the most important assets at your business’ disposal. It’s really indispensable. Not only are large amounts of it the result of successful operations, it also can help your organization better understand the intricacies of its own operations, and where you want it to go in the future. Does your business have a process for collecting, storing, and sorting vital data so that your organization can figure out where to go next?
If we asked you how your organization backs up its data, would you be able to smile and tell us all about it in detail? While it’s important to be optimistic about the future of your organization, you should never believe that you are impervious to data loss. We’ll discuss some of the most important terminology behind data backup and recovery, as well as the best way to protect your organization from the crippling situations presented by data loss.
How does your organization manage its IT? For some businesses, it’s not an easy choice or even a remotely affordable one. Some companies are forced to endure subpar services from break-fix IT providers that don’t necessarily have the tools available to prevent issues from happening. Others try to prevent issues from evolving into major concerns. These others are the organizations that have the right idea behind technology maintenance.
The modern small business will face several challenges in 2018. The world is changing, and with it, so is business. For many small businesses, this can either be looked on as the opportunity they’ve been waiting for, or, it can be viewed as the beginning of the end. No matter what situations you are faced with this year, understanding what problems your business faces, and how to solve them is imperative to your small business’ success.
All businesses require at least some type of software in order to perform as expected. It’s how organizations acquire this software that has a considerable impact on cost. For some, software can be a budget-breaking nightmare, but others have found a much more convenient way of acquiring this software: as a service.
IT maintenance is something of a sensitive topic for some organizations. While most understand that it needs to be done, they often don’t have the resources to make it happen, either due to a limited budget or timeframe. How does your business handle IT maintenance? If your organization is having troubles managing its annual technology budget, or if you are consistently experiencing profit-sapping downtime, consider managed IT services the answer to your problems.
In terms of identity theft, data loss and good ol’ fashioned pickpocketing, the holiday season is one of the riskiest times to travel. When it comes to protecting your personal information, thieves and cybercriminals are counting on you to be distracted and make careless mistakes. In 2016, the number of fraud attempts went up by 31% during the holiday season. In addition, credit cards, mobile devices, and open Wi-Fi are common targets throughout the holidays.
Digital payment options have become commonplace in today’s society. In fact, ever since people could purchase goods and services off of the Internet, some of the world’s most successful companies are a result of digital payment. It was a natural progression then, as the mobile device boom came, that mobile payment would take the place of cash and/or cards and bring these digital payment options beyond the Internet, and into our retail stores. This simply hasn’t happened and here are four reasons why.
Telephone solutions have long been a major pain point for businesses. Smaller organizations attempt to get the most bang for their buck, especially for something as important as communications, but it’s not always so simple. How can you get the greatest return on investment from your business’ telephone solution? You can start by implementing Voice over Internet Protocol.
We’ve all seen and heard about companies and government departments that have experienced major security and data loss events. Once the event is made public, there is a media frenzy of coverage disclosing answers to questions like: Were your records compromised? How can you protect nonpublic information in the future? What should you do if you are a victim? However, as the media focus moves to another topic, the breach becomes yesterday’s news - and there is very little coverage of what repercussions and penalties those entities that were breached faced - if any.
Most businesses rely on software solutions in order to stay productive throughout the work day. Whether it’s a word processor, a spreadsheet builder, or simple data storage in the cloud, software is deeply ingrained in the modern business world. Shouldn’t your organization be taking advantage of it to its full extent? You can start by implementing Software as a Service.
If you’ve ever managed a major IT project, you’re probably well acquainted with Murphy’s Law: “Anything that can go wrong, will go wrong.” Every project is going to have some rough patches. The key to overcoming these challenges lays not with the execution of the plan, but with the preparation. Here are four things to consider when you’re planning your next long-term IT project.
For the majority of small and mid-sized businesses (SMBs), finding the right technology solution is the key to growth. According to a recent study, businesses with 250 employees or less whose primary goal for 2018 is growth cited IT systems and technology applications as their top strategy for facilitating growth. However, in order for technology to provide the most ample amount of growth for your business, they must be the right selection for your individual needs. By working with an MSP, you’ll have a team of business technology solutions experts as your disposal, at a fraction of the cost of hiring an internal IT department to find and implement the IT required to accomplish your desired growth.
“The good old days” usually refer to times long past, where things were more simple. Businesses a few decades ago didn’t have much complex technology in their office, but nowadays organizations have multiple server units and plenty of workstations--all of which need more maintenance than ever before. What’s the best way for your organization to approach IT maintenance?
Would you be surprised if we told you that cybercrime is one of the biggest threats to the success of your organization? Unfortunately, there’s no escaping the fact that your business will be under fire from all sides by security threats. One of the most notorious methods includes phishing--email scams that are designed to harvest credentials and other information from unsuspecting users.
A recent surge of hurricanes, wildfires, earthquakes, and floods have crippled major cities and devastated entire regions all over the world. In the aftermath of these events, business owners are faced with a few glaring truths - one of which is the undeniable vulnerability of their business’ future in the event of a disaster. Most of the major news outlets are reporting this figure: according to the Federal Emergency Management Agency (FEMA), 40% of small businesses never recover from a disaster. Despite all the literature and precautionary tales surrounding these catastrophic events, there are still an overwhelming amount of businesses that choose not to prepare for a disaster until it's too late.
Today’s business environment is no longer just a drab gray office setting filled with workstations lining the wall. The office is the coffee shop across the street, or the airport lobby while you’re waiting for your plane to arrive. It’s the client’s office while you’re out on a business trip, or the venue for a business conference where you make valuable connections and exchange contact information. The office has gone mobile, and your business needs to adapt to this change.
The protection of your business includes many facets. Physical security, training, and network security get most of the attention (and rightfully so), but does your business have a plan in place if those strategies fail? For the growing business, understanding that your data is an asset doesn’t have to come after you lose some. If your management team prides itself on taking proactive measures to keep business running smoothly, one element that has to be on the table is the practice of data backup and recovery.
The variety of malware known as ransomware exploded in popularity in 2016, encrypting victims’ files and demanding cryptocurrency payments to restore the data to the estimated tune of $1 billion. This may seem to suggest that large corporations and companies are the primary targets of these cyber criminals--and for some, they are.
When you delete a file off your PC, or your hard drive becomes corrupted, you just take for granted that the data is gone in perpetuity. That isn’t the case at all, and it can present problems for businesses and individuals alike. The thing is that it’s deleted, it’s gone, it ceases to exist, because you deleted it with your own hands.
Have you ever tried to manage a major IT project yourself? If you have, you know that it’s a huge time sink and that there’s a lot involved with the process. We’ll discuss four of the best ways that you can save time and resources while managing your latest technology implementation project.
You might have only recently heard about outsourced IT services, but you might be surprised to hear that they have been around for far longer than you previously thought. Even before managed IT, however, business owners and individuals alike were using the outsourced services of others to simplify operations and day-to-day tasks related to their technology management.
Wouldn’t it be great to have a fully-trained and certified staff of IT professionals sitting in the corner of your office, keeping your technology in line? Unfortunately, small businesses often don’t have the budget required to hire an internal IT department filled with security analysts and network technicians. Even if they do, they don’t have the workforce to handle all of the responsibilities of a full IT department. What’s the best way to handle your organization’s IT?
Despite the industries that can be classified as “professional services” being widely varied, many of them could find substantial benefits in enlisting support from a managed service provider. Let’s examine a few of the solutions that an MSP offers, and how these solutions could help a business achieve more during the workday.
When a hacker tries to infiltrate your network, they are doing so with a purpose in mind. Usually they are looking for specific information, like account credentials, personal information, or files that can be used to blackmail victims. Regardless, we’ll go over what a hacker can do with the information that they collect from you, and how you can best protect it from them.
Your IT is a central part of your organization’s operations, but its role has changed significantly as business processes have grown more streamlined. There are always shifts and changes in the way that businesses function which must be accounted for, especially in the modern office environment. How have these shifts affected your business’s IT management?
Who would you rather hire--an employee who comes in late, after your systems have encountered an issue, and takes twice as long to fix them as he said, or an employee who was ahead of the game, and managed to avoid issues before they influenced your business? This scenario is precisely the same one that you encounter when you weigh a break/fix IT provider against a managed service provider.
Few organizations take business continuity planning as serious as financial organizations do. The Federal Reserve Bank (FRB) and Securities and Exchange Commission (SEC), as well as the organizations they oversee, depend heavily on technology for their daily operations. For these establishments, a severe data loss event or significant downtime has the potential to cripple the economy, depending on the severity. As such, they require all of the institutions that they have jurisdiction over to meet certain business continuity benchmarks.
Technology maintenance and management is one of the major pain points of all businesses, but it comes more easily to large organizations that have large budgets. Unfortunately, small organizations are often left out, placing such an important aspect of managing their business on the back burner. How, then, can you take advantage of proactive IT maintenance without breaking your budget?
Consultation is one of those words that you take for granted because you see it everywhere. Think about it, most businesses that provide a professional service offers some semblance of consultation. For the small business owner, can you really afford to pay premium prices to “experts” for them to give you their so-called professional opinion? Besides, what do service providers mean when they use the term “consultation”?
Every business is searching for ways to improve productivity. There are now quite a few methods being used to boost the amount that each employee can accomplish, many of which revolve around technology. Admittedly, some of these methods may not be attainable for the average SMB… yet. However, as technology advances you may find yourself able to leverage some of these productivity-enhancing tools to improve the look of your bottom line.
Some organizations want to better understand the process that they use to take backups of their data and restore them in the event of an emergency. This is great, because the value of being able to do so cannot (and should not) be understated. A proper data backup and disaster recovery system could be all that stands between prosperity and failure.
Smartphones, laptops, and Chromebooks empower today’s workforce to be more mobile, and employees are often the driving force behind this. Chances are, if your business hasn’t even begun to think about your mobile IT strategy, a percentage of your staff already has.
Virtualized technology services are great assets for businesses with limited budgets. Three of the best ways that your organization can take advantage of cloud computing and virtualization services are Software as a Service (SaaS), Voice over Internet Protocol (VoIP), and hardware virtualization.
It doesn’t matter where your business is located--chances are you’re susceptible to thunderstorms. Lightning storms are very unforgiving, and they can lead to all sorts of problems for unprepared businesses. We’ll discuss some of the ways that your organization could be affected by a lightning storm, as well as how you can take measures to mitigate these dangers in the future.
Fundamentally, business is simple: if you take in more revenue than you have expenses, your company is a success. There are just so many elements to manage to ensure that revenues outpace expenses that it becomes difficult to ascertain what you can do to cut costs and see a higher degree of profitability for your efforts.
As technologies emerge and trends change, organizations face massive paradigm shifts involving the tools and methods they use to conduct business. Right now, we’re in the middle of one of the most significant shifts in decades; more and more businesses are relying on cloud computing.
Just over a third (36 percent) of businesses don’t back up business data at all, and apparently this number isn’t keeping some IT providers up at night (not the case for us). Your businesses’ data is precious, irreplaceable, and extremely expensive to lose. Let’s talk about how delicate and dangerous it is to not have it backed up.
How big a role does security play in your business’s network management? If it takes a secondary role more in favor of operations, you might want to reconsider why this is the case. After all, your organization’s critical assets--namely sensitive data like employee information, payment credentials, and usernames or passwords--all hold immense risk for exploitation from hackers. Therefore, even if you don’t fear a potential attack, you should at least consider it as a possibility.
Whenever you install software on your computer, you agree to certain terms put in place by the developer or vendor. Even free software, such as Google Chrome and Firefox, have terms that the end-user opts into during installation. One of the most important terms business owners need to be aware of are those that pertain to software licenses; if you aren’t, someone else will be.
It’s a far too common scene in businesses: an employee is working on an important project when their workstation starts acting up. Flustered, they call in the IT department, but they won’t be able to make it up to them for an hour at least. So, what’s a worker to do? Just sit there and wait? With a Help Desk solution, this wouldn't be an issue.
A business’ critical operations aren’t something that can be casually postponed. Therefore, any issues that present themselves must be attended to as quickly as possible in order to avoid wasted time and lost productivity. A Help Desk solution allows an employee to call in the cavalry, so to speak, the moment something begins to go wrong.
Once the employee contacts the help desk representative, the underlying issue can be identified, rooted out, and resolved. This can all be accomplished without disturbing other members of the business. The employee’s coworkers will not need to be disturbed by a member of the IT team coming up to troubleshoot the problem, and IT will have one less distraction from their innovating responsibilities to deal with this problem.
Finally, the employee will be able to return to their work much more quickly and easily than they would otherwise--minimizing the effects of the issue on all fronts.
If a comprehensive Help Desk solution sounds like it would be a welcome addition to your support, let us know! Reach out to us at 607.433.2200 for more information today.
When it comes to a business being successful, it’s only natural to eliminate any wasted expenses and focus on those that can serve multiple purposes. Many businesses are very good at doing this, but they overlook a great opportunity to cut costs through the consolidation of their telephony system.
While at first glance, a telephone may seem to be just a telephone, this communication technology is not quite so cut and dry. More and more businesses have embraced a Voice-over-Internet-Protocol approach to handle their voice communication needs, with benefits that have a very real impact on their business. Let’s go over some of the ways that VoIP can directly assist your organization.
Significant Cost SavingsFirst and foremost, a major benefit to VoIP is the fact that it can take a considerable chunk out of your operating budget by eliminating some or all of your existing telephone bills. Since VoIP uses the Internet to send and receive sound, you have the potential to save in the long term.
This is helped by the fact that many VoIP solutions don’t require particularly specialized hardware, meaning that you will not only be saving on the phone bill, but in some cases, you might not need to replace all of your existing equipment.
Record-Keeping and CollaborationBoth the ability to document what progress has been made and the ability to work cooperatively with teammates are crucial to a business’ success. VoIP can enable a user to do both of these things. Whether it’s used to hold a meeting, recording what was discussed, or to allow clearer communication between two coworkers working on the same project from different locations. Either way, VoIP assists in keeping the lines of communication clear.
Business owners require ubiquitous access to certain information stored on their organization’s infrastructure. Thus, there’s an immediate need to safeguard this data from any sort of impending destruction. We’ll discuss ways that you can prevent the worst when it seems like your data will fall victim to a loss incident.
Do you understand what the event logs of your network are, and how they keep your organization secure? If not, you could be ignoring one of the most basic components of network security. Event logs are important for spotting significant issues on a workstation or laptop.
They say that those who don’t learn from history are doomed to repeat it, and matters of cyber security are no exception. Threats will often follow trends, and so by reviewing what has happened in the past, we may be able to glean some insight into what will be important in the future.
In the course of doing business your organization needs to lean on its communications investments. Efficient discourse between vendors, clients, and employees allows for productive action to be made quickly. If you have recently decided to deploy a feature-rich hosted VoIP business phone platform because of its ubiquity, you have to be cognizant of how to best secure your solution. Here are three variables that help you get the most out of your hosted VoIP solution.
Set Up and Utilize Private VLANsA Private VLAN (virtual LAN) gives your organization’s IT administrator more control over your hosted VoIP solution. It acts as a single access and uplink point to connect a device to a network or server. By partitioning your network, you present your administrators with the ability to secure specific devices, essentially creating separate networks. By being able to single out devices, it makes it easier to group devices together, even if they don’t share the same network switch. A private VLAN gives your organization's another layer of security while allowing access to the same feature-rich phone system; and, it helps mitigate risk, something every business is looking for in their security solutions.
Track Your UsageNo matter what platform VoIP solution you use, there is a chance it may get hacked. Most of the hacks that businesses see are ATO attacks, or traffic pumps, which aim to utilize the target organization's phone system for calls that will cost them capital. To be sure to avoid this type of interference, tracking your organization’s call usage is a solid practice. Having an up-front conversation with your VoIP vendor about what they are doing to protect your business can be a good strategy to secure it from taking on parasitic users that drain your company’s resources.
Enable Strong Authentication ProceduresYou can’t talk about security today without mentioning access control. To ensure that only your users are able to access your hosted VoIP solution, there are several practices you can implement. You can go ahead and implement a two-factor authentication strategy, or go for the gusto and deploy a powerful identity management solution. Whatever you decide, securing your solution through all applicable manners of entry is important. This includes the physical phones on your desk, mobile applications, and anywhere access can be granted.
A hosted VoIP solution is a great service to implement for the growing business. It allows you to save money while receiving all the dynamic features you are looking for in a business communications solution. For more information about hosted VoIP, communications, or how to better secure your company from threats, call Directive today at 607.433.2200.
Let’s say you get a bill in the mail for technology support, but you don’t necessarily know why you got it. Pretty troubling, right? Clearly someone in your organization isn’t privy about the proper method of getting help for their technology, but if you regularly work with a break-fix IT provider, this kind of correspondence (and cost) is unavoidable. Thankfully, there’s a simple solution to make sure that something like this doesn’t happen again.
The aforementioned scenario is created when you expect your employees to contact tech support when they are experiencing an issue, rather than contacting someone within your organization. If your company doesn’t have someone dedicated to IT support, they might be left with no choice but to reach out to someone who can help them, whether it’s in your budget or not; especially if it means completing a project on time. How can you keep your organization from being surprised by hefty IT support invoices?
It’s clear that working with a managed service provider who offers help desk support is better for your business. Managed IT providers like Directive charge only a flat monthly rate based on your service level agreement, rather than unexpected bills for unexpected support. You don’t have to worry about a stray call from an employee accruing extra charges since, as the call is covered under your service level agreement.
Consider how much can change simply by looking at your help desk solution in a different way. If your organization is billed per call for IT help, your employees might hesitate to reach out when something goes wrong. While these intentions are noble, IT issues that go ignored can escalate into full-fledged problems that can eventually cause downtime. Workers using machines that suffer from performance issues will be less productive, causing long-term problems and creating stress for your workforce.
Give Your Staff “All You Can Eat” IT SupportA good solution to the IT support conundrum is to give your staff access to unlimited IT support so that they can get the most out of their technology and perform their tasks with minimal issue. You want an IT provider that isn’t billed per call, but one that costs a set rate every month. This means that you can effectively get as much support as you want and/or need for no extra cost. This is extraordinarily important if you want a predictable IT budget.
When it comes to using technology to improve your business, it’s hard to beat the benefits that cloud computing provides. The cloud can help to boost your functionality in a variety of ways. As a result, cloud technologies have seen explosive adoption rates--and it’s no wonder, when you consider what the cloud is capable of, and how it can benefit your workforce.
So, you’ve just finished up a huge, potentially career-altering project. Your finger is poised over the mouse, ready to click ‘save,’ when suddenly your entire project disappears. Turns out, a critical issue just killed your network, your progress, and your mood. Wouldn’t it be nice if there was a way to keep this from happening?
The scenario we just described was a classic example of the traditional IT approach in action--a problem occurs, causing progress, profits, and productivity to be lost.
The main problem with this strategy is that it’s reactionary, and gives circumstances control over your business. Besides the day-to-day hassles and shortcomings that this approach brings, there are potential dangers that threaten your entire establishment. What if a disaster struck and destroyed your entire infrastructure, or you were suddenly struck by a crippling malware attack that infected your critical data?
Without preventative, proactive action, there wouldn’t be much you could do to bounce back; and, based on what has happened to other businesses after such events, it isn’t very likely that your business would last.
However, it is very possible to reduce the risk of such events with some planning, forethought, and preparedness. When a system is built, it’s built to behave a certain way. When it behaves differently, that’s a red flag.
When your technology breaks down, can you rely on your IT provider to be there in a moment’s notice? What if you need someone to talk you through a troubleshooting procedure? During the weekday you expect them to be available, but what if you’re burning the candle at both ends over a weekend to finish an important project? Furthermore, your office might be closed, but your IT infrastructure still needs to be attended to.
The small business is under siege. Many small business owners do what they can to compete, but it seems like there is no solution for their revenue woes, as larger organizations are able to attract a larger part of the market share. This has been the case for some time, but there are market forces at work today that make it even more difficult for businesses to contend with competitors that have more resources.
Many smaller businesses look to a niche market for sustainability; and, while this seems like a decent strategy on the surface, if demand falls in that niche, you could quickly be faced with some very disheartening questions. Other businesses decide to forgo this strategy and continue as intended, relying on their people’s expertise or experience to guide them through rough patches in business. This is a great strategy until your larger competitors pilfer your organization’s talent with offers of more pay and better benefits.
The truth is that there are no easy answers on how to sustain a small business through turbulent times. For this reason, one avenue almost any small business can venture down is to make improvements in technological resources to try and mitigate the gaps in financial and productivity deficits. Technology, if leveraged properly, can build additional efficiency to your offering, making business move faster. The problem for the modern small business owner or manager is ascertaining what technology investments make the most sense for you.
Where Do Mobile Devices Fit?Mobile has been a popular discussion point in every technology-of-the-future discussion for the past ten or twelve years. This means that the future is now for mobile and while there are a lot of things to love about mobile devices, for small businesses they may do more harm than good. For the small business that has already covered their bases with a thorough mobile device management platform and a BYOD strategy, leveraging the positive attributes out of mobile will be simpler than those who are starting from scratch. Of course, it’s easier to build a bridge if you’ve already procured the materials you need, but without some idea of what you’ll use it for, what’s the point?
For a small business, mobile devices can have some positive effects on employee engagement, awareness, and for cultivating the relationships you depend on. On the other hand, mobile devices can be a hopeless waste of time, which just happens to be one of the most critical resources to manage for the small business owner. With well over 90% of a smartphone’s utility wrapped up in distractions, it seems like that is an endless amount of monitoring and management for a very little return. As long as your organization has clear rules in place to manage data dissemination, access, and communication, mobile will continue to work for your business. But, if you are just getting on the mobile bandwagon, be sure to create your mobile policies before relying on mobile as a way to build more revenue.
Too many businesses suffer due to issues with their information technology. The IT department, that is supposed to be innovating, is just too swamped down solving immediate technical problems to do so. However, if left unchecked, having an IT management deficit could swiftly create larger problems throughout your organization.
While news sources might lead the layman to believe that most issues facing the typical SMB come from cyber criminals lurking online, the reality is far less dramatic. However, this misconception makes these issues no less serious, and still things to prepare for. Let’s review some of the most common causes of technological issues in the office environment.
New technology paves the way for businesses to leverage their resources in exciting ways. Of course, it’s impossible to take advantage of these benefits if you don’t even know these new technologies exist. Therefore, to help you achieve an edge over your competition, consider how these four new technologies can enhance your business model.
Smart Virtual Personal Assistants (SVPAs)Think of SVPAs as virtual executive assistants. These "predictive intelligence" apps use voice recognition to sort through personal data from email messages, address books, calendars, and task lists in order to anticipate the next logical step and drastically boost daily efficiency. Apple, Google, and Yahoo all recently acquired SVPA apps to integrate into predictive products, from mobile apps to smart speakers, helping users get tasks done even before they would remember to do it otherwise.
Security and Privacy SolutionsA perennial on Webbmedia's list, privacy concerns remain top-of-mind for wired Americans. According to a Pew Internet and Society poll, 91 percent agree that consumers have lost control of their personal data. Adobe, Dropbox, and Snapchat have experienced major password breaches, and Target and Home Depot had credit card data from millions of customers stolen by hackers. To address these system breaches and reduce the widespread public mistrust, companies are looking to spend more resources on password security and encryption management. To assist with this, Twitter released Digits, a two-way authentication service that sends one-time confirmation codes via texts, which will be offered to mobile apps.
Internet of ThingsThanks to the Internet of Things, the world we live in is now surrounded by an unprecedented number of devices with the ability to communicate directly with one another, similar to how the Nike FuelBand connects to the coffee maker. These devices will become a vital part of our day-to-day home, work, travel, and shopping experience. The implications on how IoT devices can enhance the productivity and connectivity of businesses as only limited by imagination and the ways that these vast networks can be secured.
Collaborative SoftwareLooking to make the workday more efficient, a new slew of services combine the best of email, instant messaging, social media, and cloud storage into one platform for collaborating with co-workers. Salesforce's Chatter and Microsoft's Yammer are currently two top players in this space, and with the launch of apps like Facebook for Work, the race to further socialize the office is far from over.
The cloud has seen explosive use of its services and solutions since it was first introduced, and for good reason--it offers benefits that are too useful for a business to pass up. These benefits vary, but all serve a singular purpose: to make the user’s experience easier. Here are some of the ways that the cloud can enhance the daily operations of your business.
Security: Starting off with a critical consideration for any business, the cloud can offer improved data security. Cloud providers base their entire business on their ability to safely store your data, and so they invest heavily into their security protocols.Furthermore, you can greatly reduce the risk of a lost device leading to a security breach, as there is cloud-based software that permits you to wipe the device remotely. This prevents your data from falling into the wrong hands, whether the device is misplaced or stolen.Reliability: Cloud providers stake their reputations on the ability to guarantee service to their clients at all times. While true 100 percent uptime is impossible, a cloud provider will keep the necessary skilled manpower on-hand to resolve any issues as efficiently and quickly as possible.Cloud services also allow you to enjoy the use of resources without worrying about keeping them up-to-date. Most providers will take the liberty of implementing operational and security updates on your behalf. This leaves you free to remain productive, instead of interrupting the workflow to install another patch.Access: A cloud solution allows productivity to have a place outside of the office. If an employee gets sick, or otherwise can’t leave their home, a cloud solution gives them a way to access their work files and maintain their output.The same goes for an employee on the road. If they can establish a secure connection, the cloud will allow them to continue their progress on work-related tasks.Financial Effects: Perhaps the most enticing feature, the cloud also allows for some considerable cost savings upon implementation. Since cloud computing utilizes your provider’s hardware instead of your own, you are no longer responsible for its acquisition and upkeep. As a result, you can otherwise utilize the funds that would have been devoted to your on-site infrastructure and the not-always-considered utility bill.
Directive can help you to enjoy these benefits. Call us at 607.433.2200 to find out more about what cloud-based services we offer.
So you keep hearing about the need for a firewall, but maybe you’re not exactly sure what it is or even what it does. As a business owner, you don’t need to fully grasp the complexities of network security in order to effectively manage your company. Although, it is beneficial for every business owner to understand the basics of what a firewall is, along with a working knowledge of how it protects an organization’s IT infrastructure.
What a Firewall DoesIn its simplest terms, a firewall is software that analyzes data flowing in and out of your network. Before allowing the data through, the firewall makes sure that it doesn’t pose a threat to your system. If the data in question meets the criteria of a threat, it doesn’t get through--similar to how a roadway checkpoint works. Plus, in order to safeguard your system from the latest threats, firewall software routinely updates itself via the Internet with the latest threat definitions.
A firewall is most commonly used to analyze threats from Internet traffic, but it’s also useful for discovering threats from the traffic of your in-house network. They are also helpful for validating connection and data packets, checking for legitimate application data, and performing cavity searches on all messages going to and from your network.
You also need to know that firewalls come in varying strengths. For example, an operating system for a home PC comes pre-installed with a firewall. However, a consumer-grade firewall is woefully inadequate to handle the traffic of a company network. Therefore, businesses need an enterprise-level firewall solution that can adequately safeguard all of its servers and workstations, like what you’ll find with a Unified Threat Management solution. Another advantage of a UTM is that the included firewall is just one of its security tools; spam blocking and content filtering are additional UTM tools that are included in order to provide your business with a comprehensive approach to network security.
What a Firewall Doesn’t Do While it’s crucial for every business to have a firewall, it’s equally important for business owners to have additional security measures in place so they’re not solely reliant on their firewall solution. This means taking additional preventive security measures like backing up data, actively monitoring the system for threats, and applying security patches and updates. For your convenience, these tasks and all of your security needs can be outsourced to Directive.
A small business is just as susceptible to the many problems that face large enterprises, and the dangers only multiply with the more technology you implement in the office. The larger your network gets, the more difficult data distribution and storage becomes. The more employees you work with, the more devices that will appear in the office. The more data you work with, the more likely you are to get hacked. These are all very real risks. What are you doing to protect your company from these threats?
We’d like to present one surefire way to dodge the majority of problems associated with business technology management: outsourced IT services from Directive. We can use our proactive approach to take care of your technology so that you can focus on running your business. While we offer many different types of services, here is a brief rundown of some of our popular ones.
Data Backup and Disaster RecoveryHave you taken the time to think about what your business would do if it suddenly lost all of its data? If not, do so now. It could be much more than just a couple of months’ worth of leads put at risk. An untimely hardware failure could have lasting effects on the way that your business functions. You’ll need to replace the hardware, which could take several days, or even weeks. During this time, your business isn’t working as intended, which can severely damage your productivity. Instead of suffering from this unfortunate occurrence, you can implement a BDR to take multiple copies of your data and keep them safe for recovery at a later date. BDR is designed to eliminate downtime and take a proactive stance against data loss due to natural disasters, hacking attacks, user error, and more.
Remote Monitoring and MaintenanceMost problems with your technology can be resolved remotely, without the need for an expensive on-site visit. Managed IT services capitalize on this convenience by allowing you to get the help that you need, when you need it. This cuts out waiting for the technician to arrive on-site and keeps downtime caused by the issue to a minimum, allowing you to get the problem fixed right away and get right back to work. Furthermore, we can apply any necessary patches and security updates remotely so that you will always be protected from existing and developing threats.
Network SecurityHacking attacks and security threats will always be one of the most dangerous parts of running a business. Some of the scariest threats currently on the Internet include ransomware and botnets that enslave Internet of Things devices. Only a cybersecurity professional knows how to identify and prevent infections from known threats. We can equip your business with a comprehensive Unified Threat Management solution to limit infections on your network in the first place. The UTM includes an enterprise-level firewall, antivirus, spam blocker, and content filter.
You’re in the middle of a project when your computer starts acting up. You smack it around a little bit to see if that has any effect, but it only makes the problem worse. Suddenly, there’s a blue screen and you have no clue what to do. What happened to your data? What will happen to your project? What will you do about the workstation replacement? Read on to find out.
The aforementioned scenario is one that is common in the realm of break-fix IT. Someone’s computer or other piece of technology breaks down and they don’t know how to fix it themselves. They wind up investing in expensive IT support, but more than this, they waste valuable time and resources resolving a problem that could have been prevented. This has led innovators in the technology maintenance sector to create what’s called managed IT services, which are designed to take a proactive stand against IT troubles, rather than resolve them as they occur.
It’s More Cost-EffectiveThe more time you spend spinning your wheels on an IT problem, the more time you wind up wasting. The more time you waste, the less time you can spend on profit-making initiatives. Previously, your organization was almost certainly including IT in its budget as a capital expense, but by implementing more flexible monthly payments, you can effectively turn your IT budget into an operational expense. The end result is more flexibility in your budget as a whole.
You Have More TimeWhat would you do if you didn’t have to waste time managing or maintaining your business’s technology solutions? Perhaps you would invest time into building your brand, or maybe you would rather focus on improving internal operations and employee morale. Maybe you’d like to give out the raises that your team deserves, or invest in future innovation. Either way, you’ll have more time and resources to devote to what really matters: running your business.
Your Technology Gets the Help It NeedsToo often businesses rely on their own employees to ensure that technology gets updated. This generally happens if an organization doesn’t have the resources to hire an internal IT department to take care of their technology. In other words, when you have people who have no clue what they’re doing managing and maintaining technology, chances are that mistakes will be made and time will be wasted. By having professional technicians working with your technology, you can know with confidence that your systems are being maintained by trained professionals.
Let’s say that you receive an email from a software vendor, say, Microsoft. When you are contacted by a major company like this, do you automatically assume that it’s secure, or are you skeptical that it’s a scam? Ordinarily, it might not seem like a big issue, but all it takes is one click on an infected attachment or malicious link to infect your business’s infrastructure.
According to a Swedish cybersecurity firm called Detectify, there are major online domains that are at risk of email spoofing due to misconfigured server settings. Email spoofing is the act of sending a message, while masking the true email address that it comes from. This allows hackers to forge the sender address to suit their needs. Generally speaking, email messages don’t have automatic authentication built into them. This is something that must be configured on the server side of things.
Thankfully, there are ways to properly configure your email server, but unless you’re a hardcore techie, you run the risk of either configuring the system incorrectly, or changing settings that may compromise your security. Yet, it’s still important to keep in mind how the solutions that prevent email spoofing, work. Here’s a breakdown of the details:
Sender Policy Framework (SPF): This is a record that’s checked alongside the DNS (Domain Name System) record, in order to decide whether or not the server is allowed to send email using the specific domain. SPF uses three identifiers for its messages: softfail (accept the message, but mark it as spam), hardfail (reject the message entirely), and neutral (do nothing and let the message through unhindered).DomainKeys Identified Mail (DKIM): DKIM hashes the body and the header of the email separately, and creates a private key that gets sent with the message. Once the message is received, the key will perform a DNS request to see where the email originated. If everything adds up properly, the message is received.Domain-based Message Authentication Reporting and Conformance (DMARC): DMARC is considered the ideal solution, as it makes use of both SPF and DKIM to identify an email. DMARC’s functions split into three: reject (a full rejection, and the end-user never sees the message), quarantine (the message is stored for your review), and none (allow the message through). The idea is to either identify messages as fraudulent, or provide the system administrators with the ability to review them and make the decision themselves.You might be wondering why we’re even bringing this up, and it’s because Detectify discovered that, out of the top 500 sites on the Internet, 276 of them can be spoofed. Detectify considers servers that don’t have SPF or DMARC configured correctly to be vulnerable to email spoofing - this includes using no SPF at all, using SPF with softfail only, and using DMARC with action none. Therefore, you need to take measures to ensure that your team knows how best to identify spoofed email domains, and phishing messages in general. If you don’t, you could be placing your business in harm’s way. On top of that, you’ll want to make sure your email server is configured to not allow your email domain to get spoofed.
The best way to keep your employees from falling into this trap is by ensuring that you’ve educated them on security best practices, and to limit their exposure to such threats in the first place. This includes taking the time to explain to them how phishing threats and other security discrepancies behave, as well as implementing solutions to keep suspicious messages out of your inbox in the first place.
Is your business prepared to handle all kind of online threats? A recent study shows that it probably isn’t. According to the think tank Ponemon Institute, four out of five businesses don’t have the infrastructure or security experts they need to spot and prevent incoming cyber attacks from succeeding. This is a significant statistic that can’t be ignored, especially if you want to secure your business.
Additional findings from the study include:
Only about 17 percent of respondents claim that they have any sort of process for gathering intelligence about network threats.38 percent of companies don’t have any method of intelligence gathering at all.Other companies either have one for specific purposes, or have one that’s not spread out throughout their entire organization.Regardless, the point stands that not enough is being done to learn about, and prevent, threats from accessing business infrastructures.
The Ponemon Institute claims that businesses are experiencing, on average, at least one or more external cyber attacks every month, and these breaches are costing the businesses about $3.5 million annually.
Your business’ administration should consider whether or not it can afford to become the target of further data breaches. More often than not, we expect the answer to be “no.” Yet, so many businesses refuse to accept that they could become the target of a data breach.
The online business environment is a dangerous place, especially with threats such as viruses, malware, and worse, all hiding in plain sight. Organizations need to take advantage of comprehensive security solutions that can cover all modes of attack, but finding an affordable enterprise-level solution can be challenging for SMBs. Thankfully, a Unified Threat Management (UTM) solution provides comprehensive coverage that today’s businesses need.
Your business relies on technology to keep operations moving, but your technology relies on you to stay functional. While many small businesses will choose to forsake an in-house IT department in favor of a self-service model, this is a costly maintenance practice that could put your IT in jeopardy. Instead, your organization should invest in our managed IT services, which have the possibility to show your business an entirely new way of managing technology assets.
Instead of taking a break-fix approach to IT, managed technology services take preventative measures to keep problems from escalating into major disasters. Here are three ways that managed IT services can help your business.
Cost SavingsOne of the biggest ways you can save on your IT is by implementing managed services. Due to the way managed services work, you get a service for a monthly fee. Now, compare this to the usual way of managing technology. When your technology breaks, instead of reaching out to a company that can diagnose and fix your problems for a steep cost, a managed service provider can administer the care needed as per your service level agreement.
Furthermore, the majority of problems can be prevented through careful maintenance and management, which is something that a break-fix IT provider won’t tell you. After all, they profit from your technology consistently breaking down. Managed IT providers want to save your business money through preventative maintenance. This means minimal hardware replacements, as you’ll only need to replace technology that’s in danger of an imminent failure.
Less Wasted TimeChances are that you don’t have an internal IT department, and even if you do, it’s probably buried in work that nobody has time to get to. When there’s too much work that needs to get done, it’s easy to accidentally cut corners in order to guarantee that something of critical importance doesn’t go unanswered. One of the most frequent cut corners could include the administration of patches and security updates, which are crucial if you want to keep your business safe from online threats.
Social media is a phenomenon that has invaded the business world in more ways than one. While it might be a great way to endorse your brand and communicate with your local prospects, it can be a huge distraction for your in-house workers. A new study by communications agency, We Are Flint, claims that 84 percent of adults in the UK use social media, and two-thirds of them use it every day--be it at the office or at home.
Now that mobile devices have taken over the workplace, you need to consider the security of your business’s data more than ever before. You need to think about which devices access certain data, as well as what they do with that data. In particular, you need to make sure that only your employees can access corporate information, and there are several ways to do so.
Regardless of what industry a company is classified under, they all are responsible for upholding particular standards to ensure compliance with industry regulations. However, according to the 2016 State of Compliance survey, a shockingly high number of organizations were shown to be a bit fuzzy on their requirements.
It’s no secret that one of the best ways to improve your business’s operations is by investing in quality technology solutions. However, as is the case with any type of organizational spending, IT expenditures are subject to change. After a brief hiatus, Gartner predicts that next year will be another big year in which organizations invest heavily in new technology and IT systems.
The best laid plans of mice and men often go awry, and there is no exception when it comes to your business technology. No matter how well-thought-out your systems are, you are always at a risk of some unforeseen threat causing havoc. In order to truly be prepared for anything, you need to implement a backup and disaster recovery solution for your business.
We all know the dangers of doing business with the Internet. Even a small business has sensitive information that could potentially be stolen. While it’s important to take preventative measures to keep threats out of your infrastructure, it’s equally as important to have measures put into place that can detect threats within your infrastructure.
When it comes to cloud computing, the small business has plenty of choices. There are several different types of clouds, but depending on your business’s specific needs, you can narrow it down to three: the public, private, and hybrid varieties. Many businesses are finding that the public cloud is a more valuable asset than a private or hybrid cloud. We’ll dig into the details and explain to you what these benefits could mean for your business.
Whether we’re ready for it or not, the Internet of Things is coming, and soon. You might see all sorts of connected devices on the market today that you would never think to connect to the Internet, but it’s our responsibility to inform you that these new devices could potentially put not just your business infrastructure at risk, but even your own life.
Chances are that you’re fed up with your in-house telephone network. It may have once been necessary to communicate with your employees and your clients by using a landline, but the modern office has since moved toward a more digital alternative in the form of Voice over Internet Protocol (VoIP) telephony.
If you have an internal IT department, chances are that they’re functioning in a similar manner to a help desk team. They provide technology support for your less-adept employees, or those who encounter errors that they’re unable to resolve. Chances are that your IT department could use a hand every now and then, so here are a few ways you can lighten their help desk workload to free up time for more efficient purposes.
In the business world, you rely on agile and secure access to critical documents on a number of different devices. However, security can quickly become a problem, especially when your users have multiple devices. Is your file sharing service enough to keep your data safe? Or, if it’s not, what are you going to do about it?
There’s no doubting that data backup is a critical component of any small and medium-sized business’s infrastructure. Backup and disaster recovery is important in the event that your organization experiences a death-blow in the form of a data loss disaster. Yet, there’s some debate as to whether an on-site data backup solution can be as effective as the cloud. The verdict: both are essential.
Ransomware is an online threat that continues to develop and evolve to accommodate the motives of cyber criminals around the world. Ransomware locks down your business’s files and demands a decryption key for their safe return, which makes it difficult (or impossible) to move forward with operations. How can you prevent ransomware from destroying your business’s chances of survival?
One of the biggest concerns that business owners have with remote workers is being able to control and centralize communication. A worker in the office can be plugged right into the company phone system, but how does this translate to those who work from home some or all of the time?
To accommodate these concerns, there is an option to consider. When trying to equip a remote worker with the tools they will need to remain productive and collaborate with the rest of the team, try a softphone solution on a VoIP system.
To translate this tech jargon, a softphone is a phone that functions through software on a computer, using either the conventional phone line or Voice over Internet Protocol to transmit the conversation between the involved parties. Softphones, unlike many exclusively VoIP-based phones, do not require a physical device, and instead reside on any computing solution with an Internet connection. They often include a digitally-based number pad as a part of the program.
Therefore, it makes more sense to utilize softphones when equipping your remote worker to remain connected.
After all, as an economic business owner, financing new equipment is always a major consideration before implementing any decision, especially one that revolves around technology solutions. With a good VoIP solution, you can use traditional handsets like you have been used to, but you can also send and receive calls from any smartphone, tablet, laptop, or desktop.
Have you ever taken a broken-down workstation or server unit to a break-fix IT technician, only to have them resolve the problem and demolish your IT budget with absurd costs? For small businesses that can’t afford to hire an on-site IT department, this is a common occurrence. Thankfully, the SMB now has more options than ever before for how they want their IT to be managed, and it all starts with managed IT services.
USB technology is widely-used and you’d be hard-pressed to find an organization that doesn’t utilize USB devices in some way, shape, or form. However, these devices often harbor unexpected threats that could put the security of your entire infrastructure in jeopardy. All it takes is one infected device to compromise your network. Do you know where your USB devices have been?
Since USBs are prized for their portability, they can be used for a myriad of purposes. USB flash drives or hard disk drives can be used to transport files, both compactly or in bulk. Many keyboards and computer mouses operate with USB technology these days. That’s not even mentioning the plethora of USB dongles that are used to connect other devices to your computer.
Now, imagine this scenario. An employee finds a USB drive on the ground and, curious to find out what’s on it, plugs it into their company-issued workstation. They might do this to make sure that good technology isn’t just left lying around, or maybe their curiosity just got the best of them. Either way, the files on the device could contain executable malware that can threaten your business. In many cases, the user might not even be aware that malware has been installed on the computer, and it can spread viruses, or install trojans that allow for remote access at a later date.
In fact, there’s been a recent report from May 2016 of a $10 USB device that’s capable of logging keystrokes on wireless Microsoft keyboards and transmitting the signals over a wireless frequency. Whitehat hacker Samy Kamkar built it out of a USB phone charger, which is so commonplace these days that nobody would think twice about seeing it plugged into the wall of your office. The threat of these types of devices is so significant that the FBI saw fit to issue a statement warning professionals of their dangers. While no attacks have been found in the wild, it’s still best to take the warning to heart and apply it to your own cyber security practices.
The root of the problem--the theft of data before it reaches its destination--extends well beyond Microsoft wireless keyboards, too. Any wireless device that sends signals that aren’t encrypted could potentially be intercepted by hackers using similar techniques. This method can be used to harvest data that could lead to the theft of personally identifiable information, login credentials, or financial credentials. It’s not unlike a hacker intercepting data over an unsecured wireless Internet connection.
Technology can be a constant pain point for businesses of all kinds. Due to the ever-evolving nature of technology solutions, it’s tempting to cave in and purchase the latest and greatest innovations in the industry. Yet, does your business have the time to do so, let alone the budget? Progress can be stymied by a lack of funds and personnel, but it doesn’t have to be.
More often than not, businesses are stuck in two situations. Depending on the state of your IT environment, you either have plenty of time to implement new and innovative solutions, or you have, quite literally, no time to even consider new technology. Both situations come with side-effects that could negatively affect your organization’s operations. For example, you might have time to implement new technology, but are you ignoring the day-to-day maintenance of your internal systems?
The latter can also be a major problem. If you’re spending all of your time responding to emergencies, when can you implement new technologies that can potentially improve the functionality of your business? When you can’t even handle the solutions you already have, what’s the point in implementing new technologies? Unless you can find a way to strike a balance between the two, any efforts will be both fruitless and wasteful.
One of the best ways that your business can innovate without sacrificing functionality is by taking advantage of outsourced IT solutions from Directive. Whether you’re in desperate need of a new workstation or server, or need to implement a solution on a large scale, like cloud computing or virtualization, our trusted technicians can help. If your team can’t keep up with maintenance, we can take over this responsibility while they innovate and create new solutions for your organization.
Better yet, you can rest assured knowing that you’re getting top-of-the-line technology assistance for your organization’s systems. More often than not, businesses have to cut corners in order to make ends meet with their technology maintenance, which could include allowing end-users to service their own workstations. This is a hazardous practice, as having inexperienced users performing in-depth maintenance could be both time-consuming and risky.